On August 16, 1858, the first message sent via the transatlantic cable read: “Europe and America are united by telegraphy. Glory to God in the highest; on earth, peace, and good will toward men.” From his residence in Pennsylvania, President James Buchanan responded to Queen Victoria’s telegraphed excitement by lauding the transatlantic cable as “an instrument destined by Divine Providence to diffuse religion, civilization, liberty, and law throughout the world.” As nineteenth-century European and U.S. technological advancements precipitated global communications, they also brought about an imperial geopolitical remapping that collapsed territorial and tele-technological expansions. The following overview proposes that the social, political, and economic conditions for the development of submarine telegraphic networks primed current information channels to become technologies for control and management.
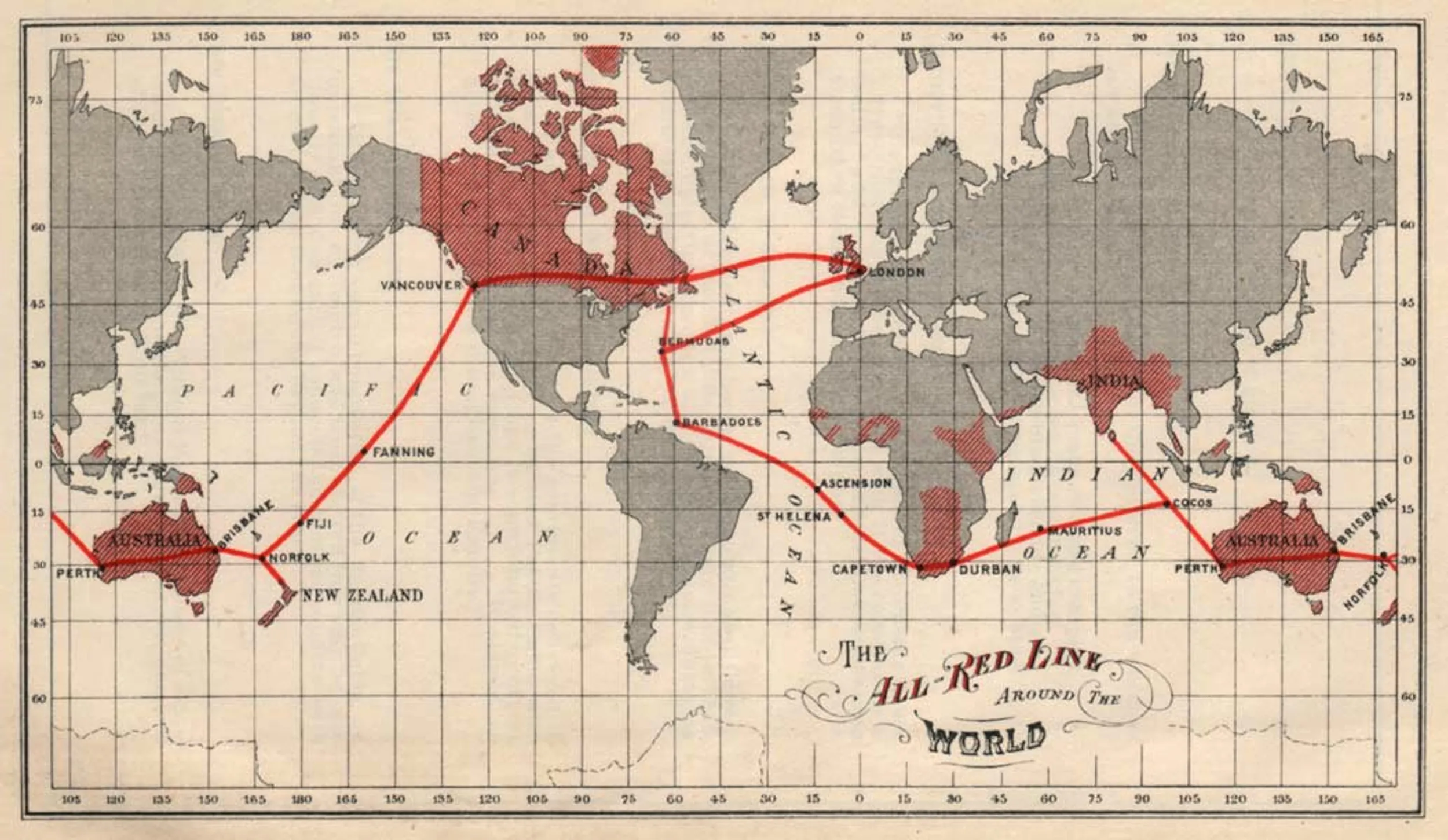
The electric telegraph demonstrated a much faster way to send and receive information than by carrier pigeon, horse, or ship. Building off the optical telegraph and earlier models that used static electricity, long-distance electric telegraphic transmissions emerged in the 1830s in Russia, Germany, and the United States. After decades of technical flops, telegraph lines were finally set up in England (by William Cooke and Charles Wheatstone) and in the U.S. (by Samuel Morse), which prodded the engineering of a transatlantic cable. Though largely unsuccessful, the fledging attempts at transatlantic cabled communications managed to amass substantial funding from British and U.S. entrepreneurs and industrialist investors despite dwindling government funding. In their respective struggles to ensure subsidies for the telegraph, both Morse and Cooke boosted its commercial value instead. The first commercial electric telegraph of 1837—the Cooke and Wheatstone telegraph—dawned what Tom Standage has called the “Victorian Internet,” a tele-communications agora in which a highly complex information economy would evolve in subsequent centuries. In 1870 the Eastern Telegraph Company connected London to Bombay, and by 1872, British imperial bandwidth reached as far as Australia, Singapore, China, Japan, and New Zealand. The Western and Brazilian Telegraph Company linked the U.S., England, and Bermuda, leading to a South American cabled expansion, and, in 1889, cables lined the coast of West Africa, reaching Cape Town. Finally, in the early 1900s, the United States connected its own territories, Hawaii, Guam, and the Philippines. While this list overlooks many cities, towns, and countries, my intention is to point out the speed and breadth of a colonial-led global telecommunications industry. In addition to quickening transnational communication between trading, news, and shipping agencies, routing these networks through their colonies and territories guaranteed the British and the U.S. empires social, economic, and political monopoly over them.
In an essay called From Cabling the Atlantic to Wiring the World, Simone Müller recounts the moment in which the transatlantic cable arrived at the thriving city of Aberdeen, in the Scottish Highlands, described in The Aberdeen Weekly as an “example of commercial heroism, which deserve[d] a wide and hearty recognition in every part of the world” given that it was “not England and America alone that benefit[ed] by it but almost every quarter of the globe.” As is the case today, access haunts all technological developments. According to Müller, even though the vast majority of Europeans and Americans could not afford to transmit a telegraphic message through the newly laid cable, it nonetheless claimed a presence in the imaginations of users and non-users alike. Müller, then, asks us to consider whose globalism was championed by the success of the “the wire that changed the world.” Applying this to today’s infrastructure, dominated mainly by the U.S., design research studio Metahaven refers to all transactions made on a Google server as events under American jurisdiction: “The United States’ global communication standards have network power. Yet, the territorial bases of these standards bind global subjects to key aspects of U.S. hard power—predominantly, its judicial regime and its pervasive surveillance, by which the United States can effectively seek to control events on foreign soil.” This affords the U.S. judicial protection over extralegal activities (such as surveillance) through the very telecommunications networks it owns.
Some argue that the postal institution provided the first blueprint for monopoly over a networked communications market that served both state and corporate actors alike. When radical Italian nationalist Giuseppe Mazzini’s fight for a unified and independent Italy in the early 1800s landed him in exile in Geneva, Marseille, and London, he had to organize riots and uprisings remotely, primarily via mail correspondence. Following the failure of one of his plans, Mazzini accused the British government of “post-office espionage” and went so far as to lace his wax-sealed envelopes with poppy seeds and strands of hair to prove that the government was opening his mail. As the result of his petition to the House of Commons, a Committee of Secrecy investigated and released a report confirming the post office’s interception. The Mazzini affair speaks to a particular relationship between governance and information. Historian Daniel Headrick ascribes the state’s need for gathering information on its subjects to a shift in power that took place in Europe at the time of its Enlightenment, when political systems moved from absolutism to enlightened despotism. Reconnaissance would have been considered essential if monarchs were to make their rule beneficial to their subjects. Driven by interests in territorial expansion and control, the spread of global telecommunications networks and information collection technologies might have been seen as a similar response to a perceived political benevolence.
If in the past security was deemed a matter of the state, today, left to surveillance technologies, it ports to the private, industrial, and corporate sectors. With networked ecosystems as far-reaching and intricately connected as corporate-owned social-media platforms, overseeing the activities of its users unites both state and corporate interests. One of the benefits of private communication technologies is that they can presumably expedite customers’ privacy over the expectation to comply with state-issued gag orders or subpoenas. But the commercial information sector also has a vested interest in mobilizing the data it vows to protect, which means corporate-state complicity ensures the survival of a live information market.
To solely attribute what privacy expert Bruce Schneier calls “the business model of the Internet” to the entrepreneurial patronage of the telegraphic cables and to the political demands of the Age of Reason and Revolution as a way of claiming that “dataveillance” is as old as telecommunications networks overlooks a crucial point. Not only does the data siphoned from users function as currency to fuel corporate interests in building consumer profiles, it also assists the government in targeting subjects for surveillance. Together, surveillance and security practices extend latent criminality beyond justifiable authorization, as evidenced by the broad and discriminatory National Security Entry-Exit Registration System (NSEERS), an entry-exit registration used by the Department of Homeland Security to observe and regulate all movements by Muslims and Arabs at the U.S. border. Much like routing telegraph cables throughout its colonial empire granted overseers the ability to assert and maintain order in their territories through telecommunications systems, watch-list databases often unjustly parse subjects into those who warrant protection and those who require surveillance. While it may seem like dataveillance has little to do with the optic regime of surveillance, it is important to remember that bodies are digitized, catalogued, and qualified based on their digital patterns and behaviors, which is the very information companies with stakes in a corporate-run cabled communications system are experts at mining. How, then, do we negotiate our relationship within these infrastructures? It might be precisely because the minority or colonized body is perpetually reconstructed as a threat by discriminatory channels of veillances that we are in fact superbly equipped to dismantle their biases. Disrupting the directionality of power inscribed in the potentate’s gaze requires a critical relooking at designs of compliance. Fittingly, in the expanded version of her 1989 CBC Massey Lectures, “The Real World of Technology,” the late activist, physicist, and researcher Ursula Franklin tasked us with the investigation of technology on the basis of its “organization, procedures, symbols, new words, equations, and most of all, mindset.” Such excavations are necessary if we are to find just uses for our tools.
Dan Bustillo is an artist and writer based out of Los Angeles. They investigate power dynamics and surveillance culture through research, letter writing, workshops, experimental lectures, and collaborative and organizational work.
This piece was originally published on publicprivatesecret.org.